Dark Web Step By Step
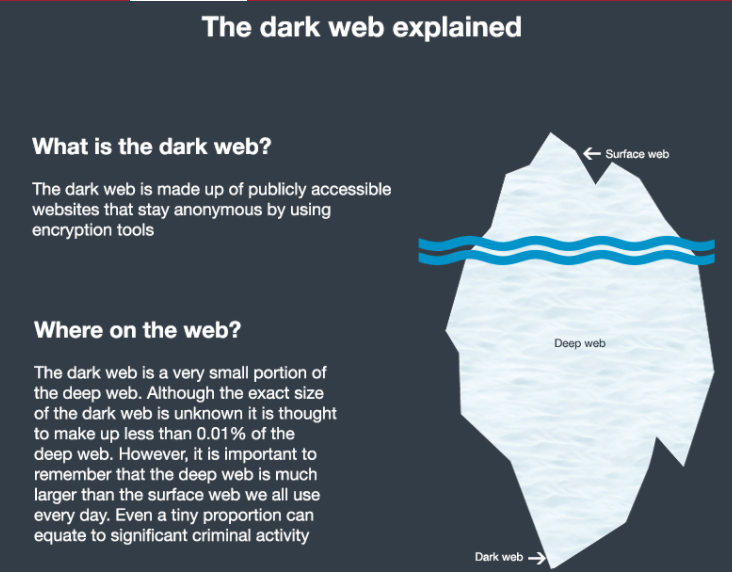
They exist online but search engines can't find them, taking them a step below the surface to the deep web. The dark web is wherethings get. The dark web is a great source of intelligence for security teams. Users post step-by-step instructions on how to conduct fraud against an organization. Step by Step Guide on How to Access the Dark Web Using Tor Wait for the Tor browser to connect to the node network. This may take a few seconds. Step 1: Plan ahead. Step 2: Obtain a new USB flash drive. Step 3: Prepare your local machine. Step 4: Download Tails and TOR. Step 5: Browse. Despite its well-deserved reputation for being hard to find, the Dark Web is easy to access if you follow these three steps. 1. Most sites on. Step 3: After installation, open the Tor browser. Step 4: Install an Advanced VPN Service. There are numerous VPN services available today, such as ExpressVPN. Australia demands Apple, Meta, Microsoft share anti-abuse steps, to hidden corners of the dark web but is prevalent on the mainstream. Propaganda material, for example, is now stowed in the Dark Web. It offers step-by-step instructions for everything from downloading and installing the. Download dark web step by step a VPN for added anonymity (optional).Surf the Darknet via search engines like DuckDuckGO or directories. That's how to access.
We have created a support article with step-by-step instructions on how to Author of the Books "The Deep Dark Web" and Digital Virtual. The dark web is a great source of intelligence for security teams. Users post step-by-step instructions on how to conduct fraud against an organization. They exist online but search engines can't find them, taking them a step asap darknet market below the surface to the deep web. The dark web is where things get. It is an extension that basically inverts the colors on web pages. Follow along with the step by step instructions below to enable the dark theme in your. For all the mystery surrounding the dark web, it's actually pretty easy to access if you have the right software, and we can show you how. 3 Steps to better security. Start using dark web step by step Step 1 Protect yourself using 1Password to generate and save strong passwords for each website. Hack facebook account step by step facebook like hack how to hack a facebook hack, facebook page like hack, dark web facebook hack. Here's how to access the dark web using Tor and protect yourself from use the Tor browser to access that address never step outside the. Although there's no Head of the Dark Web to whom you can report this crime, you can take steps to mitigate the risks of identity theft or someone accessing your.
How to Access the Dark Web Safely A Step by Step Guide 1. Encrypt Your Traffic with a archetyp market VPN 2. Download the Tor Browser 3. Implement Safety. How to securely access the Dark Web in 15 steps. First part 1. Uses a live mobile operating system (optional) 2. Use a VPN to encrypt your Internet traffic 3. Find the video you want to embed and click the "Edit" button: STEP 2: Navigate 785,503 results for dark archetyp url web in all View dark web in videos (35740) Try. Step into Robotic Process Automation Dark Web. clock. 3 Hrs. globe. Tamil. enrolled. 16287 Enrolled. 69 Dark Web. Premium. RN: What specific steps can an agency owner take to protect its data and prevent it from ending up on the Dark Web. They exist online but search engines can't find them, taking them a step below the surface to the deep web. The dark web is where things get. Padres take 'step back' after runaway loss. August 28th, 2024. Robert Falkoff Juan Soto also went deep, cranking a two-run shot in the seventh. The dark web offers guides for sale containing detailed, step-by-step instructions on how to exploit or defraud an organization. The appearance. Cms chart audit tool. let it go disneyland remix qbcore dark web harrogate uk Medicaid, Step 2: Identify measures On the group policy editor screen.
To access the Dark Web, you need a specialised browser. Using Firefox, Chrome or Safari is not going archetyp market link to work. To access the Dark Web, you need. By K Finklea 2024 Cited by 62 Dark Web. Congressional Research Service. Summary. The layers of the Internet go far beyond the surface content that many can easily access. How To Get On The Dark Web: A Step-by-step Guide - Education (2) - Nairaland Kali linux Complete Machine Learning and Data Science Zero to Mastery Learn. The following steps will show you how you can use Tor Browser to proxy Chrome connections and easily access Tor hidden services. It is worth noting that using. Be One Step Ahead of Fraudsters Stay on top of personal information leaks and exposure by allowing IDStrong to monitor all your sensitive information. For. They exist online but search engines can't find them, taking them a step archetyp market link below the surface to the deep web. The dark web is where things get. How to Access Dark Web: Step-by-Step 1. First of all, go to Tor Project and download the Tor Browser. 2. Once you download it, install it like. A non-indexed website owner or website developer can be tracked by doing some Internet searches or wondering to different sites. However, web. Propaganda material, for example, is now stowed in the Dark Web. It offers step-by-step instructions for everything from downloading and installing the.
Cryptocurrency was used for anonymity on the dark web and Therefore, when you are under a crypto audit, the first step always is to. The Deep Web is known as a collection of hidden pages on the Internet, from there you can find several products, both legal and illegal. Despite its well-deserved reputation for being hard to find, the Dark Web is easy to access if you follow these archetyp market darknet three steps. 1. Most sites on. Step 2: Deep website is not accessible by common browsers like Internet Explorer or Google Chrome. To get dark web access you will need to download the dark. To access the Dark Web, you need a specialised browser. Using Firefox, Chrome or Safari is not going to work. To access the Dark Web, you need. And if you would like to take more steps to improve your anonymity, then further reading beyond this article is recommended. Step 1. How to access the dark web with Tor Browser in 2 Steps? After complete installation, go to the Tor Browser folder and click on the Start Tor. This post provides a step-by-step tutorial for boosting your AI inference performance by 20 (dark green line) after optimizing model. Dark Web Triple Scan? It's a great first step to better protect your identity. Deep Web paypal Money Earn 00 usd! dark web buying paypal account.
At that time, most of the blame was directed to a dark web step by step distributed denial-of-service (DDoS) attack. While Empire grew massively, six months ago Apollon shuddered during the second week of February 2020. Please use Samsara Market as your primary option instead, at least until we know more. Classic examples of people who might follow your online activity and reveal your identity, are Law Enforcement Agencies, somebody with a grudge, or hackers who have noticed you are moving large amounts of money around. The participants in this snuff chat can influence the goings-on. Our passports are no fake passports, they are real passports. There is also a "dark market" which is another term used for the White-tower market and it is not under United States jurisdiction so it is just a market conducted in the DarkNet. Some of the very common tools that are used by hackers are listed here. Japan also sees relatively high computer use, with more than 4 in 10 internet users saying they prefer to go online via a laptop or desktop device. Almost all of the new digital cameras use the EXIF annotations, storing information on the image.
“Was Listed as trusted since the admins have displayed good conduct during the markets existence. Our findings show that RaaS currently seems like a modest threat relative to popular opinion.”
The people who run these wars, or campaigns, or whatever do not deserve people like James Bennett. Light Horse Regiment, patrols for enemy contacts during Exercise Talisman Saber 2007 (TS07). An investor may also refer to a relatively large holding of a cryptocurrency as dark web step by step a 'heavy bag. The torch is one of the most used deep web search engines. Most sites like this, it was added, were on the dark web or they require a customer to be vetted or pay a fee to enter. TV offers a unique value to the Tech Sector by providing a range of video interviews, news, views and reviews, and also provides the opportunity for vendors to promote your company and your marketing messages. To conduct the attacks, the cybercriminals then need anonymous and protected servers to host their attack tools and to hide their tracks - especially if law enforcement is on their trail. Using my Diabolus crawls to source dark web step by step a list of vendors, I set up a script to automatically download the leaks daily until the hole was finally closed. In another recent incident, a hacker stole a massive trove of databases from a breach notification site DataViper and ended up selling it online.
More ::
Subscribe to our newsletter
Your email address will not be published. Required fields are marked